Pdmc
From ESS-WIKI
ARM Pelion
Pelion Device Management Client Example
This example is demonstrate how to connect to Pelion Device Management. Please follow the below steps to give it a try.
- Step01: Prepare an Mbed account
- Before a device connected to Pelion Device Management, the user need an Mbed account. please refer to the below link to sign up
- An Mbed account - "sign up if you don't have one."
- Access to Pelion Device Management - "request access here"
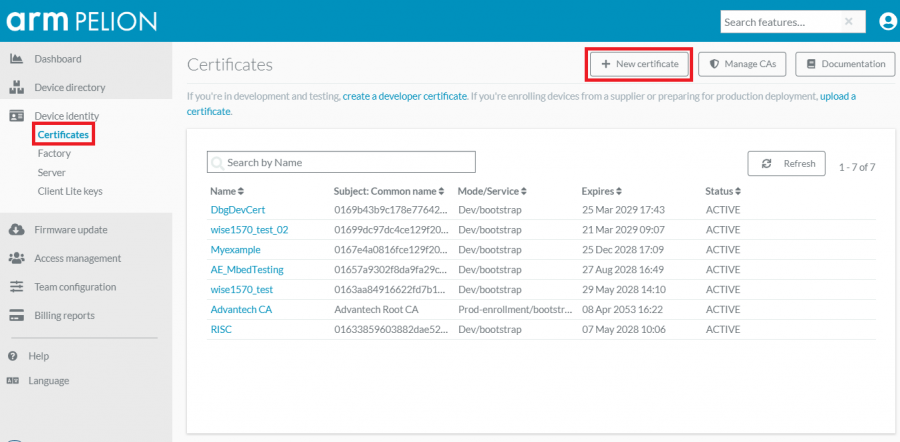
- Step02: Create developer certificate.
- Please click "link to create certificate" and follow the below steps to create a new one.
- Click the "New certificate"
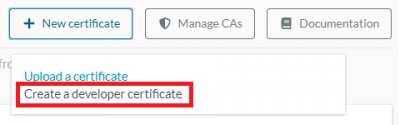
- Click the "Create a developer certificate" in pop-up window
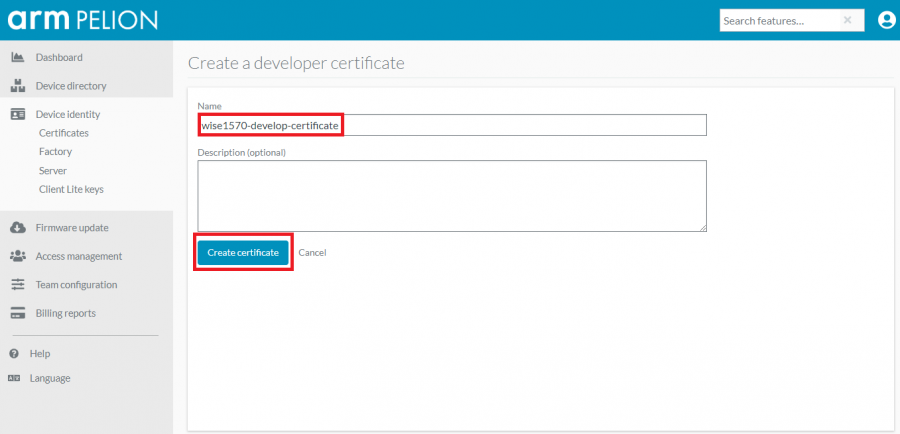
- Give a name of your certificate
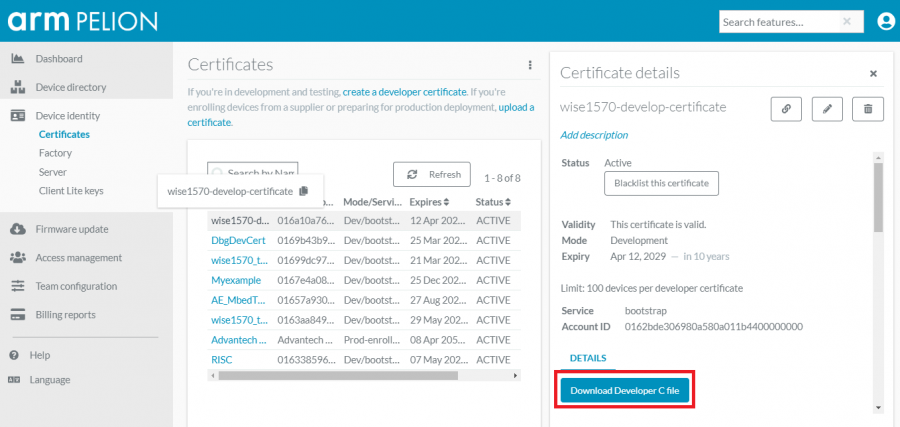
- Click the "Download Developer C file" to download the certificate
- Replace the file "mbed_cloud_dev_credentials.c" to your source tree before the process of build the hex file in Step03
- Step03: Get source code and compile it by mbed CLI.
- Please click "Link to source" and review the file "README.md" to know how to deployment and compilation with this example. The output hex file will be "source_dir/BUILD/WISE_1570/GCC_ARM/WISE-1570-Pelion-Device.hex"
- Step04: Flash programming by DAPLINK using WISE-DB-1505
- Check device connected to PC using micro-USB cable and use drag-and-drop programming with your hex file.
- Step05: Access sensor data in Pelion Device Management Portal"
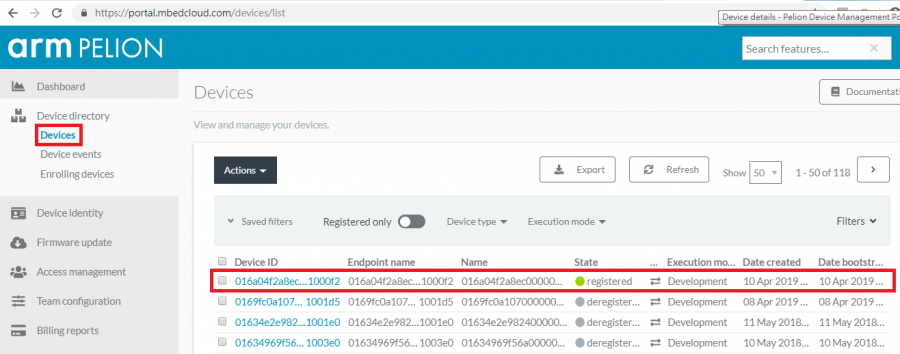
- Open browser and go to "Device Management Portal's Device Directory page.". The user will see the list of devices.
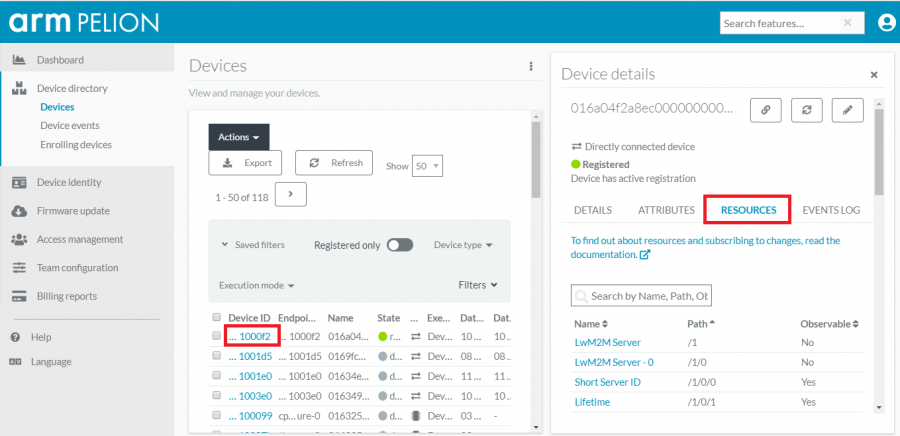
- Click the device ID and select the "RESOURCE" tab to view the device's exposed LwM2M resources.
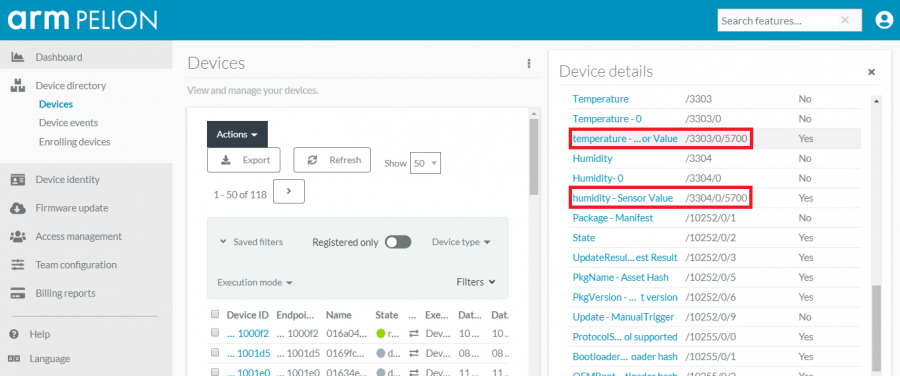
- Scroll down to locate the resource temperature or humidity.
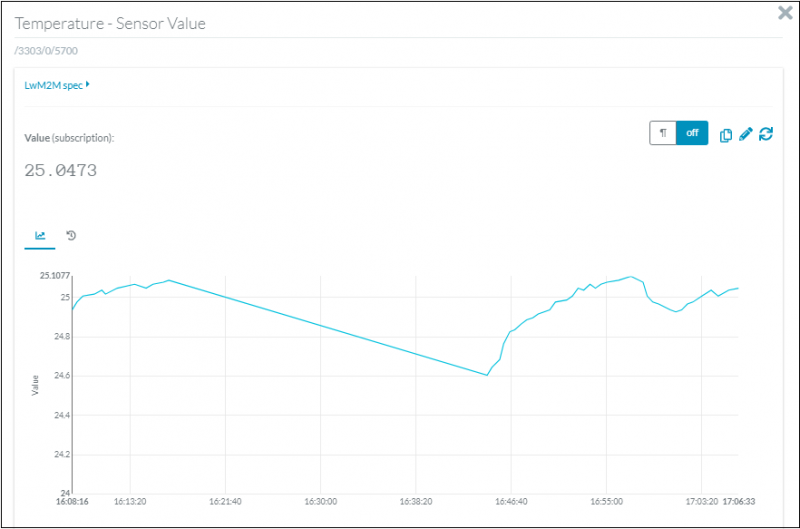
- Click "temperature - Sensor Value" or "humidity - Sensor Value" to open the graph and observe the sensor's data changed.
OTA with PDMC
The “Over the Air” (OTA) is method for software update. For PDMC, we use the manifest tool to demonstrate how it works. Please follow the below steps to give it a try.
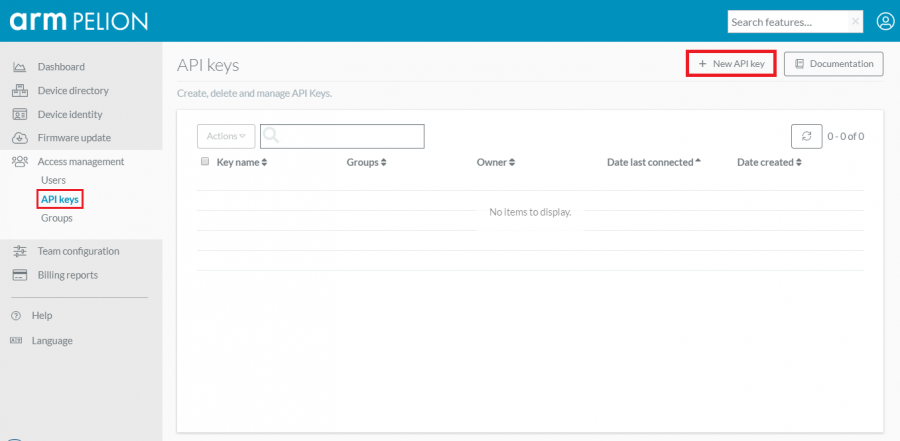
- Step01: Create an API key on Pelion Device Management Portal
- Click the "New API key"
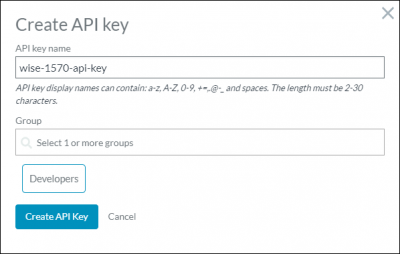
- Give a "API key name" and select the "Developers" group
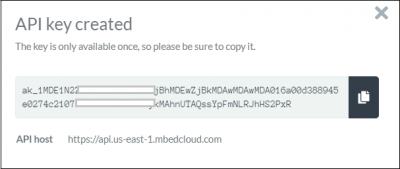
- Copy the API key and API host, then save it in your PC
- Please note that the key is only available once, so please be sure to copy it.
- Step02: Install manifest tool
- The manifest tool is compatible both with Python 2.7.11 and later and with Python 3.5.1 and later.
- Option1: install from PyPi with pip
$ pip install manifest-tool
- Option2: install from GitHub over HTTPS.
$ pip install git+https://github.com/ARMmbed/manifest-tool.git
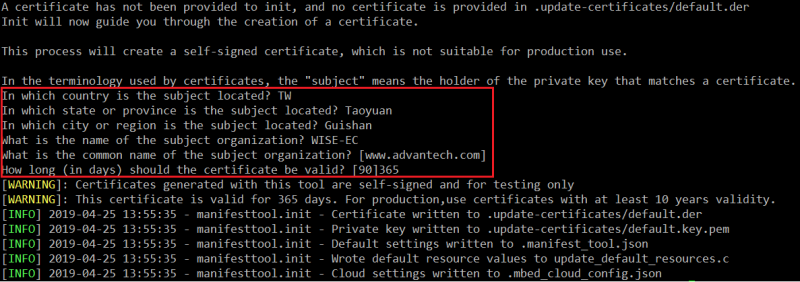
- Step03: Create a new project
- Initialize by manifest-tool.
$ manifest-tool init -d "<company domain name>" -m "<product model identifier>" -a "<Device Management API Key>" -S "<Device Management Alternative API address>"
- Example:
$ manifest-tool init -d "www.advantech.com" -m "wise-1570" -a "ak_1MDE1N2ZmZTA5ZGEzMDAaMjBhM12wZjBkMDAwMD87MDA016a00d388945e0274c21077000000004bkctykMAhnUTAQssYpFmNLRJhHS2PxR" -S "https://api.us-east-1.mbedcloud.com"
- Fill in the information.
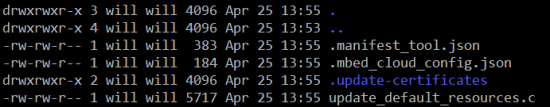
- Output files
- Step04: Add certificate into source tree and rebuild the PDMC
- Please replace the file "update_default_resources.c" generated by manifest tool into your source tree.
- Build out the hex file and it will be "source_dir/BUILD/WISE_1570/GCC_ARM/WISE-1570-Pelion-Device.hex"
- Please replace the file "update_default_resources.c" generated by manifest tool into your source tree.
- Step05: Flash programming by DAPLINK using WISE-DB-1505
- Check device connected to PC using micro-USB cable and use drag-and-drop programming with your hex file.
- Step06: Build the new PDMC that has "OTA" string displayed on console
- Comment out the macro "OTA_TEST" in main.cpp and rebuild the PDMC.
- The output binary will be "source_dir/BUILD/MTB_ADV_WISE_1570/GCC_ARM/WISE-1570-Pelion-Device_update.bin
- Comment out the macro "OTA_TEST" in main.cpp and rebuild the PDMC.
- Step07: Launch OTA
$ manifest-tool update device -p <payload> -D <device ID>
- Example:
$ manifest-tool update device -p WISE-1570-Pelion-Device_update.bin -D 016a04f2a8ec000000000001001000f2